Hvad kan man bruge en Windows-CD til?
Vel, her er et forslag.
Microsoft og en del andre arbejder i øvrigt på et nyt
"sikkerhedsløft", der kaldes "trusted computing".
Dette betyder dog ikke, at du som bruger vil kunne stole på de
programmer, der kører på din computer - det betyder, at
producenterne kan bestemme, hvad du må og ikke må på din
computer. For eksempel kunne "trusted computing" bruges til at
forlange, at alle programmer, der kan gå på nettet, skal have
indbygget en "bagdør", der kan tillade leverandøren eller regeringen
at overvåge al kommunikation.
Eller, som det også forklares her:
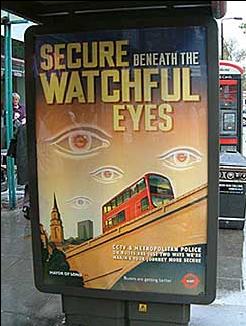
The Trusted Computing Group (TCG) is an alliance of Microsoft, Intel, IBM, HP and AMD which promotes a standard for a `more secure' PC. Their definition of `security' is controversial; machines built according to their specification will be more trustworthy from the point of view of software vendors and the content industry, but will be less trustworthy from the point of view of their owners. In effect, the TCG specification will transfer the ultimate control of your PC from you to whoever wrote the software it happens to be running. (Yes, even more so than at present.)Endnu en grund til at bruge Linux og anden fri software, der giver en fornuftig og praktisk platform for den, der efter bedste evne vil undgå den eskalerende Big Brother-mentalitet!
The TCG project is known by a number of names. `Trusted computing' was the original one, and is still used by IBM, while Microsoft calls it `trustworthy computing' and the Free Software Foundation calls it `treacherous computing'. Hereafter I'll just call it TC, which you can pronounce according to taste. Other names you may see include TCPA (TCG's name before it incorporated), Palladium (the old Microsoft name for the version due to ship in 2004) and NGSCB (the new Microsoft name). Intel has just started calling it `safer computing'. Many observers believe that this confusion is deliberate - the promoters want to deflect attention from what TC actually does.
(...)
There are some gotchas too. For example, TC can support remote censorship. In its simplest form, applications may be designed to delete pirated music under remote control. For example, if a protected song is extracted from a hacked TC platform and made available on the web as an MP3 file, then TC-compliant media player software may detect it using a watermark, report it, and be instructed remotely to delete it (as well as all other material that came through that platform). This business model, called traitor tracing, has been researched extensively by Microsoft (and others). In general, digital objects created using TC systems remain under the control of their creators, rather than under the control of the person who owns the machine on which they happen to be stored (as at present). So someone who writes a paper that a court decides is defamatory can be compelled to censor it - and the software company that wrote the word processor could be ordered to do the deletion if she refuses. Given such possibilities, we can expect TC to be used to suppress everything from pornography to writings that criticise political leaders.

